Infinispan Security #2: Authorization Reloaded and Auditing
Since the last post on Infinispan Security, there have been a few changes related to how we handle authorization in Infinispan. All of these are available in the recently released 7.0.0.Alpha5.
Authorization Performance
Previously we mentioned the need to use a SecurityManager and javax.security.auth.Subject.doAs() in order to achieve authorization in embedded mode. Unfortunately those components have a severe performance impact. In particular, retrieving the current Subject from the AccessControlContext adds, on my test environment, 3.5µs per call. Since the execution of a Cache.put takes about 0.5µs when authorization is not in use, this means that every invocation is 8x slower.
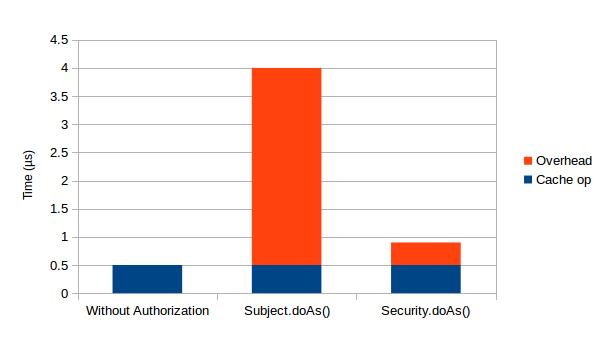
For this reason we have introduced an alternative for those of you (hopefully the majority), that do not need to use a SecurityManager and can avoid the AccessControlContext: invoke your PrivilegedActions using the new org.infinispan.security.Security.doAs() method, which uses a ThreadLocal to store the current Subject. Using this new approach, the overhead per invocation falls to 0.5µs: a 7x improvement ! Security.doAs() is actually smart: if it detects that a SecurityManager is in use, it will fallback to retrieving the Subject via the AccessControlContext, so you don’t need to decide what approach you will be using in production. The following chart shows the impact of using each approach when compared to running without authorization:
Auditing
An essential part of an authorization framework, is the ability to track WHO is doing WHAT (or is being prevented from doing it !). Infinispan now offers a pluggable audit framework which you can use to track the execution of cache/container operations. The default audit logger sends audit messages to your logging framework of choice (e.g. Log4J), but you can write your own to take any appropriate actions you deem appropriate for your security policies.
As usual, for more details, check out the Security chapter in the Infinispan documentation and the org.infinispan.security JavaDocs.
News
2020-09-08 Infinispan 12.0.0.Dev03
2020-08-31 Non Blocking Saga
2020-08-28 The developer Conference Sao Paulo
2020-07-28 Infinispan Server Tutorial
2020-07-27 Infinispan 12.0.0.Dev01
Tags
Tags: